UPDATE 11.30, 25/1/19
The blue button phishing attack appears to be dissipating although we are still resetting user accounts if we discover they have been compromised. The vast majority of blue button related ingoing and outgoing email was blocked by approx 12pm yesterday but it took the best part of the rest of the day for the Information Centre to work through the backlog of resets and blue button related enquiries.
We are now in a position to close the Major Incident in UniDesk. Those attached to the call will receive a final communication from us. When our investigations into the incident are complete, we will publish a summary report on our blog which will be linked from the Staff Roundup and the Student Bulletin.
This attack has exposed the university community to the realities of a fairly sophisticated phishing attack. Despite all of the technical measures we have in place to prevent an attack like this, ultimately the security of the network comes down to the people using it. We urge all users to make themselves familiar with our Information Security advice on UniDesk and to follow our IS News Blog and Twitter to see current Information Security alerts as they happen.
If you want to test your ability to detect a phishing email, try this quiz by google.
UPDATE 15.25 24/1/19
IS has now blocked incoming and outgoing blue button emails, so the volume of these should reduce rapidly. Since we instigated the block at lunchtime, over 9,000 emails have been blocked. Many students and some staff will find that their network account may have been disabled during the course of today – this is because we acted quickly when we discovered your account was compromised and reset it.
If you find yourself locked out of your account, please try to discover it at https://portal.stir.ac.uk/discovery. If you get the error message ‘Account already discovered’, please contact the Information Centre for advice.
We are still analysing the impact of this attack but believe that something in the region of 300 students/staff clicked the blue button. When it comes to cyber security, an organisation is only as strong as its people so we must all learn to be more cyber aware. Unfortunately this means becoming inherently suspicious of email correspondence even if it comes from your friends/colleagues. If something doesn’t seem sensible (e.g. why would a student/staff member send you an email with a button which then asks for your password??) then don’t trust it. Trust your gut.
We believe, at this stage, that assuming you have changed your network password, that should be the breach contained. If this changes we will inform users what to do.
This morning Information Services has received several notifications from Office365 that a number of student accounts have been compromised. These accounts have spammed the university address book from the compromised accounts so any member of staff or student may receive a ‘blue button’ email.
How did the accounts get compromised?
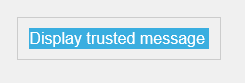
The owner of the student account clicked on a link (blue button) in a scam email. Most of the examples we’ve seen this morning contain a blue button with wording: ‘display trusted message’. If you click the link you will be taken to a seemingly innocuous web site like the BBC via a login screen which may be branded to look like a Stirling uni page (e.g. have the uni logo on it). If you enter your password into the login page, your account has now been compromised and the spammer will start using your account to propagate the blue button emails to everyone in your address book and the global address book.
The blue button looks something like this:
The subject line of the email can be ANYTHING – many of them are clever enough to appear like replies to actual emails you have sent.
What action has been taken to deal with compromised accounts?
Microsoft Office365 (provider of our student accounts) is automatically blocking outbound email from compromised accounts when a suspicious level is reached. The Information Centre receives a notification of this and we immediately disable the network account of the account concerned. We are now blocking inbound and outbound blue button emails so the volume should drop off but please continue to be vigilant.
What to do if you clicked a blue button
Did you click on the blue button? If so, immediately reset your network password via the portal home page or here: https://portal.stir.ac.uk/security/change-password.jsp
You may find that your account later becomes disabled if we receive a notification from Microsoft and follow our process to disable your account.
If in doubt, please contact the Information Centre to get advice.
What to do if you’ve received a blue button email
As long as you haven’t clicked on the blue button, you don’t need to do anything. Just delete the email.
If you have any questions about this or need advice, please contact the Information Centre.
REMEMBER – these buttons can be any colour (the last attack in December were green). More often than not suspicious links don’t even have a button 🙂
THINK BEFORE YOU CLICK.
Information Centre
01786 467250
Or log into UniDesk via the portal and click ‘Contact Us > Ask IT’
